Vulnerabilities in IoT security camera open the doors to … everything. Who would have thought that installing a smart IoT security camera could leave you so exposed?
Avira researchers have found that the PC530 Wireless Security Camera from Victure can do more than what you would ever expect – or want – from a smart security device. It comes with built-in vulnerabilities which enable hackers to manipulate device functions, step into your home network, watch your activities, and upload whatever they see onto the internet. And it’s not just the end user that should be concerned. This device is also vulnerable to being drafted into a botnet army and joining a DDoS attack to knock others off the internet.
Who is watching who?
Internet Protocol (IP) surveillance cameras such as the Victure PC530 are mainstay IoT devices. Their ability to watch human activity make them a perfect residential or commercial surveillance tool. Features ranging from face recognition to various image sensors and connectivity options ranging from Bluetooth to WiFi make them highly attractive and easy to install.
The sheer number of connected cameras and their expanded capabilities have also made them an attractive target for cyber criminals – especially when many of these cameras have significant security issues. According to SAM Seamless Networks, security cameras make up nearly 47% of the most vulnerable smart devices. Thanks to their physical positioning in buildings and their in-built weaknesses, hacked security cameras can cause an exceptional loss of privacy and security. It’s not watching out for you – it could be watching, recording, and broadcasting everything you do.
Mission control, we have a problem
At Avira, our researchers regularly look into smart home IoT devices to uncover their strengths, weaknesses, and vulnerabilities. This enables us to better protect our users, their devices, and design more effective security tools. After analyzing the PC530 Wireless Security Camera from Victure, we found four significant security issues. Here is a fast-paced introduction to each vulnerability and why they are important to the individual user with a technical explanation of the findings.
- Here are the house keys – Permits unauthenticated telnet access with root privileges
- Take a look, take pictures, share them too – Allows the interception of password and video stream -RTSP protocol
- You’ve been drafted into a botnet army – Vulnerable to the gSOAP service Integer Overflow issue
- What? I don’t hear you – Corporate responsiveness and responsibility
Here are the house keys: Unauthenticated telnet access with root privileges
The PC530 permits unauthenticated telnet access with root privileges. It’s like handing a person on the street your house keys. Once telnet is accessed, the stem is exposed and the device can become a platform for malicious activities. Although, the file system for such devices is generally read-only, they have an option of adding a SD card for storing data such as video and audio recordings, which can be used for malicious purposes like acting as a beachhead for penetrating the local network, downloading spying tools, or even running malware. This scenario is demonstrated below:
Using the PC530 for network reconnaissance
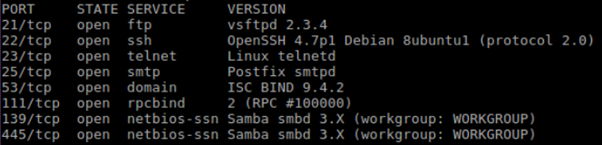
In order to demonstrate how camera can be used by a hacker as an attack vector to penetrate into the network, researchers ran Nmap (a free and open source network scanner) on the camera. The camera then scanned the network, identifying open services which could be subsequently exploited.
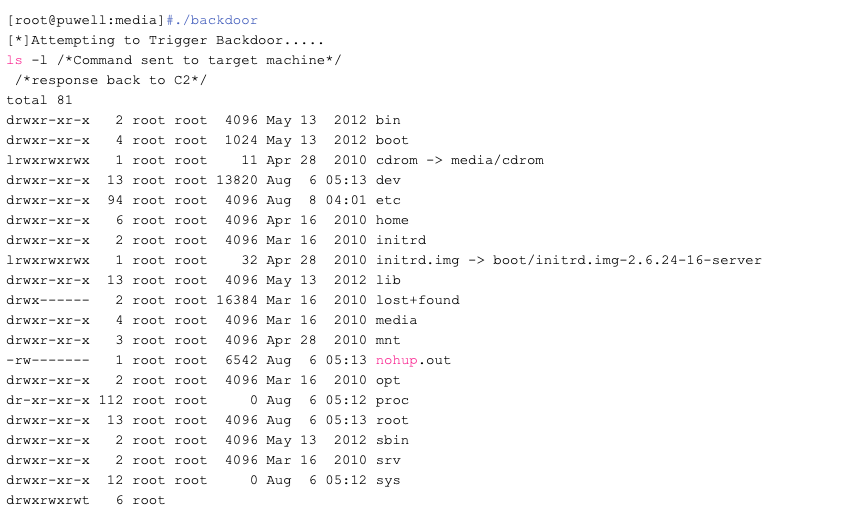
Penetrating and exploiting other systems on the network using the PC530
They found that the ftp service was vulnerable to vsFtpd Backdoor Command Execution and this could be exploited. To replicate a real-world scenario, they sent a Linux command to a vulnerable system in the network, and received back a response to the CnC (in this case, the camera):
Take a look, take pictures, share them too: Intercept password and video stream with RTSP protocol
The PC530 supports ONVIF software along with the Real Time Streaming Protocol (RTSP) when the device is streaming. Although this is not the default choice on the device, RTSP does come with weak credential authentication and is vulnerable to man-in-the-middle interception of the password and video stream.:
A dictionary-based attack was used to extract the username and password of the camera enabling researchers to access the live video stream. Victure has already mentioned that there is an unencrypted traffic with ONVIF set on, which is a security risk.
- G711ALAW-media-1.wav
- G711ALAW-media-2.wav
- H264-media-2.264
- H264-media-4.264
Researchers also found that ONVIF Manager allows the RTSP address to be found and the URL played via Media Player without authentication – thus exposing the RTSP to the internet. This was accomplished as a proof of concept by running TCPdump on the camera and forwarding the RTSP traffic.
Yes, you have been drafted: gSOAP service Integer Overflow Vulnerability
Further analysis led to the uncovering of the device’s vulnerability to gSOAP Integer Overflow CVE-2017-9765. This allows for remote code execution and the denial of service. Researchers were successfully able to create a denial of service:
Pid 135 is the process responsible for handling camera functions. The image below demonstrates it is no longer operating. A carefully crafted input file (payload) to camera may result in remote code execution.
What? I don’t hear you: Corporate responsibility and responsiveness
Avira received no response from Victure after attempting to contacted them repeatedly about these vulnerabilities in the PC530 Wireless Security Camera. We followed the industry standard practices for not publicly disclosing vulnerabilities without first allowing the device manufacturer to fix the security issues. Bugs are an intrinsic part of IT. Developers and manufacturers (Avira included) all benefit from outside researchers uncovering bugs and vulnerabilities – and making timely responses to these discoveries. The seriousness of the previous three vulnerabilities are compounded by Victure’s nonresponsiveness. It’s not good for users and it is not good for the IoT sector as a whole.
Secure the device or the home?
As the Victure camera shows, when it comes to picking an IoT device, users are at a disadvantage. It’s hard to find out what products have vulnerabilities, what patches are out there, or even how or if a device can be updated. There might even be an array of no-name devices embedded into a security package.
Given this situation with a huge range of unknown devices and limited consumer IT skills, we believe the key to home security is not just at the individual device level – whether this is an IP camera, thermostat, or TV – but at the router level where the home is connected at the internet. This is why Avira has been developing SafeThings, a solution that secures connected devices in the smart home directly from the router, and are soon to launch routers with IoT security in partnership with TP-Link. More news to come later.
Technical details
Device Name: Wireless Security Camera
Model: PC530
Manufacture: Victure
Firmware Version: 3.13.70
CPU: Grain Media GM81355
Application:iOS & Android
WiFi LAN Frequency:2.4GHz,WPA2 encryption, IEEE802.11b/g/n
SD Card: Max support upto 64G
Required actions
Avira researchers recommend that the vulnerabilities in the Victure PC530 smart cameras be addressed in the following four steps:
- Fix unauthenticated telnet access with root privileges.
- Build stronger authentication mechanisms.
- Encrypt sensitive data (video and audio streams) even alongside with ONVIF service set. Use SRTSP used instead of RTSP.
- Fix the gSOAP service Integer Overflow Vulnerability.
This post is also available in: German