Rosetta is a new way to create Flash files, which made possible a new kind of vulnerability affecting many websites, including very popular ones.
 Scenario: you’re using (for example) LinkedIn…
Scenario: you’re using (for example) LinkedIn…
 …but you accidentally visit a malicious website…
…but you accidentally visit a malicious website…
 …that wants to take over your LinkedIn account.
…that wants to take over your LinkedIn account.
It’s common for any website to be able to receive some information from other external websites: for example, it’s used by the “Like” buttons (Facebook, Twitter, Google+…) you see often on other external websites. A common method to receive information is to do a request to the target website, and give as a parameter your own function, that will be called back by the target, and will receive JSONP (JavaScript Object Notation with Padding) formatted data. It’s commonly called a JSONP request.
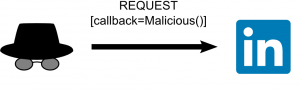 The malicious site can do a JSONP request to LinkedIn, and give its Malicious() function to call back, as a callback parameter.
The malicious site can do a JSONP request to LinkedIn, and give its Malicious() function to call back, as a callback parameter.
LinkedIn then returns the JSONP-formatted data by calling Malicious() (in the context of the malicious page).
Malicious() can only read the information that LinkedIn sends: it can’t modify information and it can’t control what is sent. This explains why JSONP requests are commonly used, even if it could look an information leak: when implemented correctly, it’s not a security risk in itself, because external websites can’t control the information that is sent. But if a Flash file was passed as a callback parameter instead of a function like Malicious(), it could have more control, because it could be executed by the browser in the context of the target site (and if you’re wondering why, that’s just because that’s how Flash works). To prevent that, JSONP requests only accepts printable characters in callback parameters
._0123456789 abcdefghijklmnopqrstuvwxyz ABCDEFGHIJKLMNOPQRSTUVWXYZ
 and a Flash file usually contain many non-printable characters, so they can’t be used as a callback parameter.
and a Flash file usually contain many non-printable characters, so they can’t be used as a callback parameter.
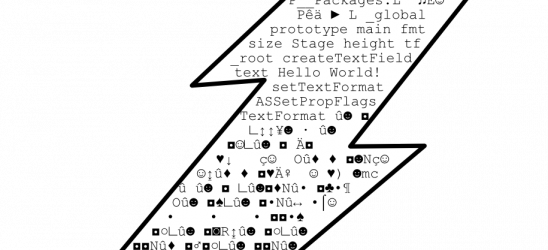
Enters the Rosetta Flash vulnerability, known as CVE-2014-4671.  With complex tricks, it’s actually possible to make a Flash file made only of printable characters.
With complex tricks, it’s actually possible to make a Flash file made only of printable characters.  By using such a Flash file as a callback parameter,
By using such a Flash file as a callback parameter,  the Flash file is executed by the browser, in LinkedIn’s context: this gives control to the malicious website over the LinkedIn page’s information. It affected many major websites:
the Flash file is executed by the browser, in LinkedIn’s context: this gives control to the malicious website over the LinkedIn page’s information. It affected many major websites:
LinkedIn, eBay, Google, Instagram, Twitter, YouTube, Baidu, Tumblr, Flickr, Yahoo! …
A simple way to prevent this for a website is to prepend a comment (such as /**/) at the start of the callback parameter: this will prevent the callback parameter to be interpreted as Flash, as Flash files are not allowed to start with comment characters, even with Rosetta.














