Rokku is a new variant that comes with its own characteristics, too:
- The cybercriminals have learned from their “user experience” during the last years.
- Rokku follows on the trail of Locky & Co ransomware.
- The cybercriminals are really professional and have a single goal in mind: How to make their victims pay the ransom.
But why?
Rokku’s spreading mechanism is quite similar to that of all the other ransomware cases we have seen. The malicious program is spread via emails that are nearly perfectly written, closely targeted to the recipient, and which convey the feeling that this is very important! We call these campaigns “Spearphising”.
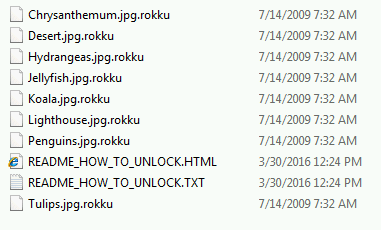
The infection strategy itself is also very thorough, a fact that supports my statement about these cybercriminals working very professionally. First off, it will delete all your shadow copies, done by the technology included in Microsoft Windows which allows taking manual or automatic backup copies, to make sure that you will never be able to recover your files after the encryption. Then Rokku does what it does best: Encrypt all images and documents on your hard disk and/or mapped networks drives with a RSA-512 crypto algorithm.
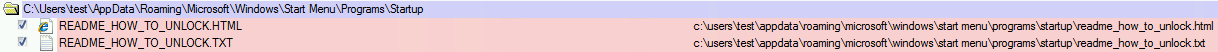
After encryption, all traces of the malicious program on the system have been removed. There are only references about how users can get their files back.
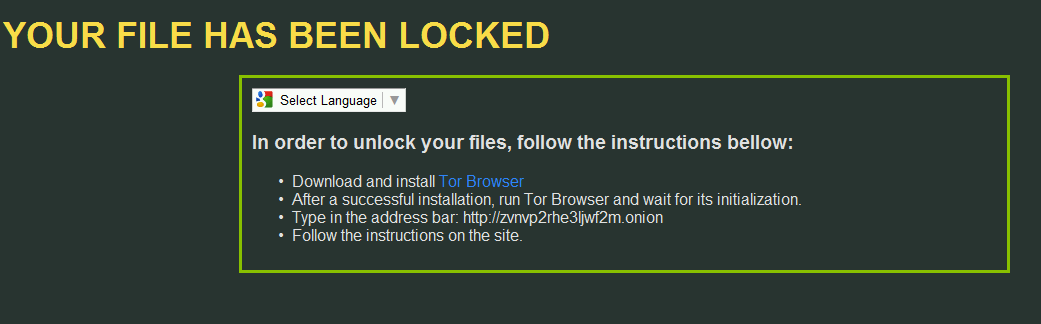
As an additional feature, the Rokku developers even let you select a language on the landing page. This enables them to reach more people: language / translation barriers just aren’t an issue any more. In the past, the text was only offered in English or – if you were very lucky – in your native language based on your geo-location.
The links provided by the bad guys are onion addresses and relate to TOR (anonymity network). This means they must be opened with a TOR browser. If followed, a page with a perfect “look and feel” pops up and explains all the steps needed to get your encrypted data back.
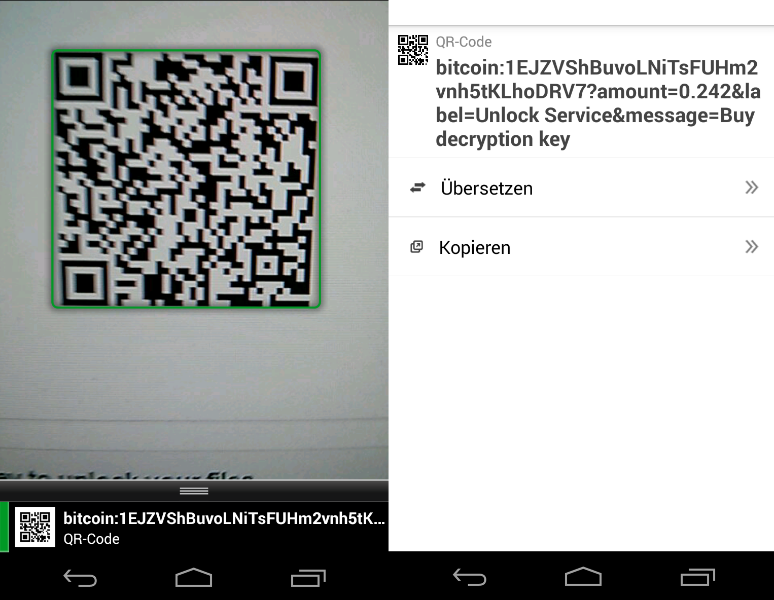
It’s the QR, not the Da Vinci Code
What I really want to highlight though is the QR Code on this page. It’s the first time that I have seen cybercriminals give their victims the possibility to use a QR Code to send the bitcoin ransom their way.
Here’s what it looked like on my smartphone:
The QR code will open up a Google search query, which explains how to get the needed amount of bitcoins.
Searching for the answer
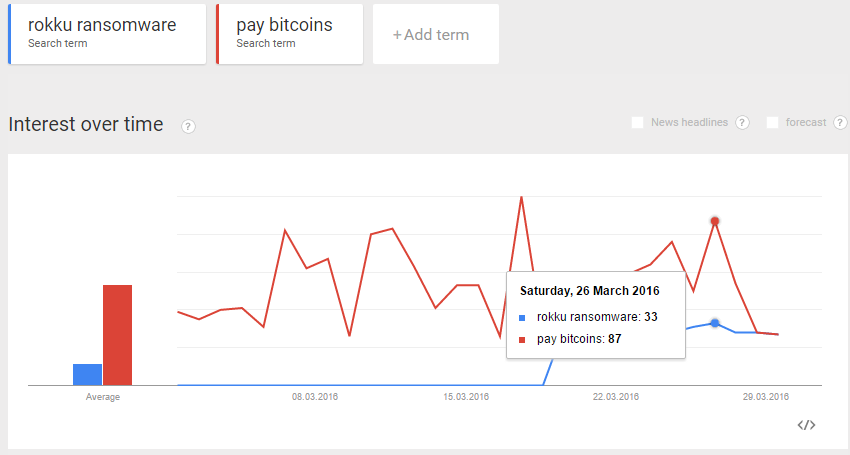
Since Rokku has been released a week ago, the popularity of these search terms, as well as the question “…paying bitcoins…” has increased significantly. It is quite interesting to see how ransomware creators may be aware of this search trend. They take great care to make sure that everyone understands how to get the needed bitcoins and even include the links! It looks like they really want be a “user-friendly malware”.
The most asked question from my friends, relatives and even my dentist … is: “Should I pay the ransom?” Although I was able to unlock one file for free by using their decryption tool, this does not ensure that the rest of your files will be unlocked after you pay up. Therefore: NO! Don’t pay. EVER.
By the way: Avira detects this threat as “TR/ Genasom”.