Right since it was founded, Facebook, in particular, has been combating fake profiles, bots, and attempts to crack into user accounts. In recent years, however, these attacks have become ever more sophisticated and ingenious. In the most well-known scam, complete profiles are cloned and then used to fraudulently obtain money and codes for money transfers or direct debits from the victim’s friends. While it may sound like an obvious trap, sadly people fall victim to them all too often.
A less obvious way, but one which is still doing the rounds, to hijack user accounts is to gain access to them by guessing or rooting out the password. This could be an acquaintance who knows the actual password and wants to get one over on the person – but it could just as well be a cybercriminal. For them, social network accounts are particularly interesting, especially if the target is also an administrator of a company website. As soon as access has been gained, the attacker can then control the website and unleash untold damage. Even access to email accounts, online banking services, and many other platforms can be obtained under certain circumstances.
Two-factor authentication
It’s precisely for these reasons that an increasing number of companies are offering two-factor authentication. The key aspect here is that alongside being asked to enter your regular password, another method is employed that relies upon using a completely separate device wherever possible. The aim is to ensure that only the authorized user can actually access his/her account. In addition, the user is informed simultaneously about each login attempt and may take further action if, for example, there is suspicious activity on the account.
Methods
Text codes are probably one of the most common methods used by private individuals for two-factor authentication. If you want to log in to your Google account, for instance, you first enter a password and then you receive a code on your smartphone. Only by also entering this can you access your account.
Code generators are also popular, although these are used mainly by companies for their employees in order to protect sensitive data. Here, an external device or app generates a new code each time a user logs in. The user then needs to input this code.
Another variant, which is used frequently on smartphones, is additional fingerprint security. Many banking apps and payment service providers now offer this function.
On top of this, more and more methods for semi or fully automatic authentication are being introduced particularly in the business environment. Here, the user can either unlock his/her work computer or other things via Bluetooth or the NFC chip in smartphones or access cards.
Drawbacks
Despite the additional layer of security, two-factor authentication also has some drawbacks you need to be aware of before switching over to using this system. For one thing, a separate request is typically generated each time a user logs in, meaning the process takes longer than just entering a simple password. If you frequently switch between accounts or use a lot of devices, this can get really annoying.
On top of this, you need to have the preferred method of generating a code with you at all times. If you selected text authentication, and you don’t have your smartphone with you or there’s no reception, you can’t access your account. Things are just as problematic if you lose your smartphone or if it breaks.
Plus points
Arguably the greatest plus point is the additional layer of security. While two-factor authentication can’t protect you against every possible attack, it does make life much more difficult for criminals. For anything work-related, and especially when it comes to your own money, you should go for this option regardless of the possible drawbacks. This aside, even minor inconveniences in terms of personal (data) security shouldn’t put you off.
See the platform provider’s help pages for information about setting up two-factor authentication – such as those from Google and Facebook.
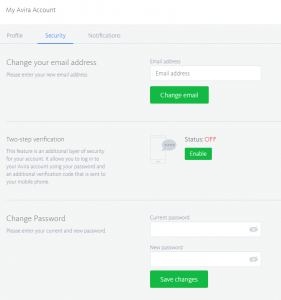
By the way, every My Avira Account comes with two-factor authentication, which you can enable really easily via the control panel.